|
Social engineering most commonly occurs when hackers manipulate employees into voluntarily parting with an organization’s funds. Hackers take advantage of human nature to exploit a target organization through its employees. Social Engineering usually involves an email or other type of communication that induces a sense of urgency in the victim, which leads the victim to promptly comply. By educating staff to be alert to these tactics, organizations can reduce the risk of falling prey to such schemes. Social Engineering Fraud Techniques
Reduce the Risk of a Social Engineering Fraud Loss
Claim ExampleAn employee received emails supposedly sent by a project manager for a large construction project. The emails instructed the target to ‘update’ the wire instructions for a routine payment, to a new (fraudulent) account. Unfortunately, the project manager’s email account had been compromised, allowing the bad actors to send and receive emails from a legitimate email account. The payment request was also sent on the Friday before a holiday weekend, with no staff available in the project manager’s accounting department to confirm the change in wire instructions, as they were attending a holiday party. What made it work? The emails appeared legitimate, as they were sent from a recognized email account. The good nature and trust of the employee to accomplish their task in a timely fashion, coupled with a lack of adequate verification procedures led to a social engineering fraud loss of $6.2 million. Cyber InsuranceCyber risk mitigation involves taking proactive steps to protect against and reduce the adverse effects of the key risks to your organization. Implementing network security defenses, incident response plans and employee training are all essential elements of cyber risk mitigation. Unfortunately, this is not enough. The reality is, no organization is immune from a cyber-attack, regardless of the strength of their defenses. This is where insurance can help. Comprehensive stand-alone cyber insurance will help protect the organization’s assets by transferring some of the costs associated with the inevitable breach. Cyber insurance complements and supports active security measures by providing third-party regulatory and liability insurance as well as a host of first-party response, remediation and recovery insurance. In addition, most cyber insurance providers also provide free or discounted pre-loss services to assist an organization in breach preparedness. Cyber Risk Management Tips
Crime InsuranceCrime insurance provides first-party coverage intended to help an organization recoup loss due to employee dishonesty, theft of money or securities, robbery, burglary, forgery and alteration, and faithful performance of duty. In addition, Crime policies should also include coverage for Computer Fraud, Wire Transfer Fraud and Social Engineering Fraud. Many of these coverage extensions require additional underwriting beyond a typical renewal application to be included within a Crime insurance program. Today, many stand-alone cyber policies may also include similar or identical coverage extensions. This means there is a potential for overlapping and/or redundant coverage. Organizations should strive to coordinate insurance coverage between stand-alone cyber and crime policies in order to ensure they are able to maximize potential insurance recoveries and eliminating any gaps in coverage, in the event of an incident. In addition to the above, most crime policies also provide a limit for investigation costs for covered loss, assisting the insured in paying for the complex process of determining the extent of the loss once the fraud has been uncovered. Coverage is typically on a loss discovered basis, meaning that the cumulative loss over time, regardless of when it took place, is covered by the policy in place when the loss is discovered. Crime Risk Management Tips
As more and more public agencies embrace the use of Unmanned Aircraft Systems (UAS) or drone technology, there is the potential to increase the organization’s liability and exposure to loss. Examples include errant drones striking a person or object and causing injury or property damage, or allegations related to privacy issues to name a few.
Recreational UseUnder the FAA Modernization and Reform Act of 2012, Congress established a special rule for “model aircraft,” which the FAA has interpreted to mean a UAS (or drone) operated for hobby or recreational purposes. For example, an individual that uses a UAS to take photos for personal use would fall under these rules. However, if that same individual took photos with the intent to sell them, this could be considered commercial use. Under the model aircraft rules, a recreational UAS must operate in accordance with a community-based set of guidelines, such as the Academy of Model Aeronautics (AMA), fly below 400 ft. above the ground, within visual line-of-site of the operator, and must receive approval to fly within 5 miles of an airport. There is no pilot certificate requirement, however, recreational users must register the aircraft if it weighs over 0.55 lbs. Civil (Commercial) UseOperations that are for commercial, business, or non-recreational use fall under the Civil Use category. The FAA implemented Part 107 of Title 14 of the Code of Federal Regulations, known as the Small Unmanned Aircraft Rule. Prior to Part 107, commercial UAS use was prohibited by law unless an operator received a special exemption from the FAA, known as a Section 333 exemption. Civil operators that received this exemption may continue to operate under those provisions or they may choose to operate under the Part 107 rules. Part 107 created a new type of pilot certificate, known as a Remote Pilot, and provides detailed rules for the operations of civil unmanned aircraft within the National Airspace System. Some of the major provisions of Part 107 include:
Many of the restrictions outlined in Part 107 are waivable with permission of the FAA if the applicant demonstrates that the operation can be safely conducted under the terms of a certificate of waiver. A summary of the Small Unmanned Aircraft Rule (Part 107) can be found on the Federal Aviation Administration website - here. Public (Government) UsePublic Use involves operations performed for a government entity, such as law-enforcement, fire department, public-funded universities, etc. These operators have the choice to operate under the FAA’s Small Unmanned Aircraft Rule (Part 107) or can apply for a Certificate of Authorization (COA). COAs are typically customized to the operation being requested by the public entity and may allow special provisions that would not be authorized under Part 107 rules. The COA outlines in detail the parameters under which the operations must be conducted and operators must follow the restrictions outlined in that document. Current COA holders may be viewed - here. EquipmentTo help minimize losses related to the use of drones, public agencies and utilities should give consideration to choosing equipment that has state-of-the-art safety features such as automatic return-to-home safe mode in the event of low battery or loss of control signal; collision avoidance technology; and GPS geo-fencing. Once the UAS is selected and purchased the FAA requires that it be registered if weighing over 0.55 lbs. - Registration link. Remote Pilot RequirementsThe FAA requires that all operations under Part 107 be conducted by a Pilot-in-Command (PIC) that holds a Remote Pilot Certificate. While the rules permit a PIC to allow another un-licensed individual to manipulate the flight controls of the aircraft, they must always be in a position to take back control of UAS. In order to qualify for a Remote Pilot Certificate, an individual must:
Although not required for FAA certification, an operator should also receive flight instruction in the operation of their particular UAS. This should include training in preflight inspection, general operations, configuration of safety features, and emergency procedures should the aircraft become unresponsive. PlanningThe FAA requires that, prior to every flight, the Remote Pilot conducts preflight planning. This includes items such as: assessing the operating environment and considering the risks to persons and property, checking local weather conditions, checking airspace or flight restrictions, ensuring that the aircraft is in a safe operating condition, checking the control links, and ensuring that the aircraft has enough available power for the duration of the flight. In an effort to balance the increasing use of UAS with safe operation, regulations continue to change. To help you use UAS in a safe manner, it is important that you follow the UAS manufacturer’s recommendations as well as keep current on regulations by visiting the Federal Aviation Administration website - here. InsuranceMost general liability and excess liability insurance policies include an aircraft or aviation exclusion, which would preclude insurance coverage for a UAS (Drone). This exclusion may be amended to provide coverage for a UAS (Drone) operations by providing the drone(s) used and pilot(s) credentials to your liability insurance program underwriter. Resources
The possibility of a costly abuse claim arising is a very real threat for public agencies that provide care or services to vulnerable populations, including children, the disabled and the elderly. Abuse can take a variety of forms as it can be sexual, emotional, physical, or even financial in nature. Year after year, camps, schools, youth recreation leagues, after school programs, daycares, among others, face the staggering financial cost of civil judgments due to the abusive conduct of their employees or volunteers. While organizations can mitigate their exposure to incidents of abuse through proper risk management, no organization is ever immune to abuse claims. With this in mind, it is imperative for organizations to understand what role insurance can play in relation to liability arising from actual or alleged abuse. What are the risks?In recent years, organizations in the religious, education and public service sectors, have been propelled into the spotlight because of lawsuits stemming from allegations of sexual misconduct or abuse toward minors. Sexual misconduct, molestation and abuse are serious liability issues for any organization, but certain organizations are especially at risk if it is frequent, unsupervised interaction between children and adults. While you may not think instances of abuse and molestation will occur at your workplace, the reality is that every employee and volunteer represents a potential risk. What's more, many employers are often unaware they can be held liable for the harmful actions of their staff or volunteers, whether it be bullying, abuse or molestation. Let's examine some examples:
Situations like these are not only common, but they can also cause irreversible damage to an organization's financial well-being and reputation should litigation occur. And while you may think your existing insurance will protect you in the event of a claim, the truth is that standard liability insurance policies often offer insufficient coverage often exclude coverage for abuse & molestation. Gaps in Traditional InsuranceFor a period of time, many insurance policies did not contain exclusions with respect to liability arising out of cases of abuse and molestation. However, in the 1980s, following a dramatic rise in civil and criminal actions against religious and secular organizations over crimes committed against children, insurance companies began to limit or exclude coverage for acts of abuse and molestation. Although the exclusionary language found in policies varies by insurance company, typical insurance coverage does not apply to "bodily injury" or "property damage" arising out of claims of abuse or molestation. Accordingly, if an organization's insurance policy contains an exclusion of this type, claims against an organization for abuse are not likely to be insured. Abuse and Molestation InsuranceWith the introduction of the abuse and molestation exclusions, many insurers began to offer new options for abuse and molestation coverage. This coverage, which is subject to underwriting requirements, may be added as an endorsement to a traditional general liability policy. Under this type of insurance, covered claims of misconduct may include actual or threatened abuse, molestation or sexual harassment. Organizations with the proper insurance can be covered for compensatory damages, judgments, settlements, statutory attorney fees and defense costs. The Role of Risk ManagementAs a condition for obtaining abuse coverage, many insurance companies require organizations to demonstrate that they have implemented a formal abuse prevention plan. When reviewing applications for coverage, underwriters look for certain elements in abuse prevention plans, including, but not limited to:
More InformationWhile it should be the goal of every organization to prevent incidents of abuse from occurring in the first place, the reality of operating in today's world means that organizations need to be prepared for the worst. Should a situation develop that requires an organization to defend itself against claims of abuse, the cost of doing so can be debilitating.
In order to protect your organization's future, it is vital to obtain the proper insurance. Set up a consultation with one our insurance experts to evaluate your risks and ensure you are covered accordingly. Unfortunately, employees and members of the public get hurt at our facilities. Alas, solutions to this problem are not always simple. Effectively reducing the probability of workplace incidents and third-party injuries and property damage requires a comprehensive approach to safety and risk awareness. Ergonomics, engineering, biomechanics, industrial hygiene, inspections, and other areas of occupational safety and health must all be considered in working toward a solution. All of these disciplines focus on the physical workplace and its “fit” with the worker – work tasks are redesigned, layouts altered, tools customized, workstations tailored, tasks analyzed, and new step-by-step processes developed. The remaining piece, however, is worker performance. If you continue to identify and act on opportunities to optimize the work environment and develop worker capability, but your incident rates haven’t improved, perhaps you’ve forgotten to address the human element at its most basic level – behavior. Studies have shown that people tend to repeat a behavior that has positive consequences, even if the behavior itself is not productive or “safe.” Are your workers continually removing the guards from their machines, running through the shop, or neglecting to wear their safety goggles, or cutting corners for the sake of time, speed or efficiency? It may be because they are praised or otherwise rewarded for something other than safety (e.g., speed). At-risk behavior can have positive, if unintended, consequences for the person performing it. The net result is that the behavior is repeated. A program to reward safe performance is one way to focus on and reinforce safe behaviors. When well designed and administered, a Safety Incentive Program can contribute greatly to your overall incident prevention efforts. Why Incidents HappenWhen a worker is injured on the job, the first natural question is “What factors contributed to this?” Incidents reflect discrepancies in the workplace; in other words, something in the worker’s environment was not right. Most incidents can be attributed to one or more of the following three basic discrepancies:
Employers can ensure that workers are thoroughly trained in safe procedures; they can provide appropriate, well-conditioned tools and personal protective equipment (PPE). While performance discrepancies can be more challenging to control, positive consequences for safe, productive behaviors can be managed. How can you “make” your employees work safely? Why People Fail to Perform SafelyIt’s really quite simple... people fail to perform safely because their immediate work environment does not support the safe behavior. Behavioral psychologists have explored two factors that influence behaviors: antecedents and consequences. Antecedents are the factors that occur before the behavior and influence its occurrence. Consequences are the factors that follow a behavior and influence the probability of the behavior occurring again. Consequences, whether positive or negative, are extremely powerful in shaping human behavior. The most successful behavioral change programs focus on rewarding positive behavior rather than punishing negative behavior. If you can identify the consequences in your workplace that support unsafe behavior and replace them with new consequences that encourage safe behavior, then you can begin to decrease performance discrepancies. Establishing Your Incentive ProgramSafety Incentive Programs or Safety Performance Reward Programs can fail, or seriously backfire, if they are poorly planned or executed. For example, consider what might happen if your program consisted of rewarding workers each time they collectively achieved 30 days without an incident. The safe workers would be punished for the unsafe acts of others (if an incident occurred that negated the reward), and all workers would be likely to underreport incidents to avoid spoiling the group’s record. Possible Rewards:
It is appropriate to provide group rewards for achieving major safety goals, but most of the rewards in an effective Safe Performance Reward Program should be small, frequent, and based on specific, individual acts of safety. Steps for a Successful Incentive ProgramTo ensure the best chance for success, follow these eleven steps when establishing your reward program.
When entering into any kind of contractual arrangement with a third party it is important to ensure that proper and consistent risk transfer procedures are in place to help protect your entity from potential liability or damages caused by that contractor or service provider. If these procedures are not in place or followed consistently, your entity could be responsible for damages if the responsible party does not have adequate insurance coverage. This article is intended to help outline the steps needed to prevent or limit liability to your entity when entering into contractual agreements. Assign ResponsibilityDetermine which department or employee/s will be responsible for managing the contract review and risk transfer process. It is recommended that this process be centralized so that insurance requirements, waivers, etc., are being collected consistently. In different agencies, this process may be handled by different individuals – risk managers, legal department staff, finance directors, human resources directors, etc. No matter who is authorized establish, review and approve contracts, they must ensure that consistent risk transfer procedures are adhered to for each contract and service agreement. This includes one time and ongoing contracts. If a decentralized process is used for smaller contracts, with department heads for example, then a copy of each contract should be reviewed and maintained periodically to ensure procedures are being followed. As a reminder, all new contracts and service agreements should be reviewed by legal counsel to make sure they do not expose your entity by limiting their own liability. Review Current PracticesEvaluating where you stand with contractual risk transfer can be time consuming but it is necessary to get a full understanding of where you may have gaps in your protection. Create a list of all active contracts and service agreements for each department and determine where you are currently obtaining Certificates of Insurance (COIs), naming your agency as an additional insured, obtaining hold harmless agreements, and to ensure the adequacy of insurance policies and limits are acceptable, among other criteria. Review ContractsOnce you have a complete and thorough list of your contracts you can determine where you have gaps that are not consistent with your requirements so that upon renewal that contract can be amended. Moving forward those contracts should include the following risk transfer protections in all bid specifications. Certificates of Insurance (COIs)A COI from the contractor's insurance provider serves as evidence of what current insurance is in place. This helps ensure that their insurance policy will respond first. Verify the COI contains the following:
Other Certificate of Insurance considerations:
Certificate of Insurance Retention Retain the COI on file for the State’s statute of limitations plus one year. For example, if the statute of limitations is two (2) years, keep COI on file for three (3) years. If a claim is involved, it should be kept with the claim indefinitely. The reason is, if a vendor has done something problematic and gone out of business, the entity still has a way and the necessary time to resolve the issue and financially become more whole for themselves or for a resident/customer who may have been affected by negligence. Hold Harmless AgreementsHold Harmless Agreements or Indemnification Agreements are separate from a COI and should also be obtained prior to entering a contract. Hold Harmless Agreements help provide protection against claims that could arise from the contract work or service being provided. These agreements should only be entered into once the organization has consulted with your own legal counsel regarding:
Waiver of Subrogation ClausesIn most cases, state laws require that general contractors are responsible for losses incurred by subcontractors. Thus, by signing a contract with a Waiver of Subrogation Provision, you could limit your insurance company from collecting or bringing a possible subrogation action that can recover damages that result from negligent acts and/or poor workmanship of contractors, architects, and/or subcontractors. The Standard AIA construction contracts presented to some public entities may contain a Waiver of Subrogation provision (usually at Section 11.3.7. ) that contains the following: The owner and contractor waive all rights against: 1.Each other and any of their subcontractors, sub-subcontractors, agents and/or employees of each other.2. The architect, architect’s consultants and separate contractors as described in Article VI. With this provision in place, increased exposure to losses can be caused by the following:
To prevent losses it is necessary to review all contractual agreements thoroughly prior to signing. All contract agreements also need to be reviewed by your legal counsel and any noted Waiver of Subrogation language must be agreed to prior to approval and final signature. Please note that some contractors and/or subcontractors may alter standard provisions through "Supplementary General Conditions” or “Addenda” to the contract. Resources
Large capital projects involve years of planning, by engineers, architects, and project managers, among others, to construct critical infrastructure as part of our systems. Within the planning process, it is important to evaluate the risk management and insurance implications that these projects can have on our organizations. Large construction projects present risks in several areas, many of which may not be apparent at the outset of a project:
While contractors perform most, if not all of the work on large projects, project owners are often named in claims and involved in subsequent litigation when incidents occur. Shielding your organization from third-party claims is key, and most effective when we have comprehensive insurance and risk management requirements embedded in our contracts. Coverage AnalysisAre we requiring the appropriate types of liability insurance policies from the contractor? Some liability policies are often overlooked – automobile liability for the use vehicles, environmental liability, if the project could impact our drinking water utility or a neighboring utility, or professional liability for engineering, design and other technical experts we contract with. Liability Insurance LimitsBasic liability limits are often the default when contracts are prepared. The liability limits we require should be established commensurate with the risks of the project. Some of our greatest risks may arise from very small elements of the project, or from activities that seem innocuous. Many of the largest third-party liability claims in this area have involved demolition contractors, excavation contractors and even contracted street sweepers. One incident involving a contracted street sweeper resulted in a catastrophic accident with 3 fatalities and total claim costs of over $10 million. Additional Insured StatusMany of us are familiar that as the owner of a large project, our organization should be listed as an ‘Additional Insured’. Additional Insured endorsements extend our contractors insurance policies to protect us as project owners, if we are named in claims arising from their work. What we may not realize is that there are several nuances to additional insured status that we need to be aware of. There are dozens of Additional Insured endorsements, and unfortunately there is not a single endorsement that adequately protects a project owner against all claims. To remedy this situation, we should request that we are listed as an additional insured for both ongoing and completed operations. Also, most of the additional insured endorsements now state that as the additional insured, you are only entitled to access the liability insurance limits that you required, not the liability insurance limits that a contractor ultimately purchased. This could result in a shortfall in the insurance limits available to protect you in the event of a large claim. Builder's Risk InsuranceBuilder’s Risk Insurance policies are a form of property insurance, protecting facilities under construction against direct physical loss. While it is not uncommon for project owners to leave the responsibility for the builder’s risk insurance to the general contractor, project owners should be involved in settling the coverage parameters of the builder’s risk insurance. There are many areas that can be incorporated in the overall insurance program that are not standard, some of which include:
There are many other areas to address when evaluating the insurance and risk issues for large construction projects, but hopefully this will serve as a primer to have more detailed conversations in your own organizations about how to most effectively prepare for the unexpected during major construction projects.
Public Officials have many duties and responsibilities as stewards for their cities, counties, districts, and other public agencies. In the discharge of those duties there are circumstances to avoid, which could lead to a public official errors and omissions claim. Public Officials claims are the least frequent type of claim that occurs with public agencies. Claims are based upon an allegation of a wrongful act, error, or omission on the part of a public official. When a claim arises it typically is very costly to defend and settle, with an average litigation time of 6.5 years, and an average defense cost of $1.1 million. Most public officials claims arise the following areas:
Conflicts of InterestConflicts of interest may be active, such as an official doing work that could benefit from a board/council/commission decision. Many years ago, a Mayor and City Council voted against a competing development that was planned for their community, to ensure that their planned development would benefit from the lack of competition. Other examples include elected officials failing to disclose that a relative may benefit from the sale of surplus property or other assets. Conflicts of interest may also be more subtle. These circumstances can be difficult to convey, particularly when decisions may benefit those that we work with or that we associate. The key to avoiding a public officials errors & omissions claim is it to have a process set for disclosure of potential conflicts of interest. After disclosure is made, officials should recuse themselves from any discussions in question. Public officials may want to error on the side of caution, as the open meeting record may be perceived differently than their intent. Disparate or Discriminatory Treatment To assure fairness in the delivery of services, it is essential to have clearly defined policies and procedures. The policies and procedures define the methodology and application of services and assure that resource allocation is established by a priority that is clearly defined. A good example is the maintenance and repair of roads, where a clearly defined procure for road repair is outlined and followed for the application of capital assets and routine maintenance. In the absence of a clearly defined procedure, road work or repair may appear to be arbitrary, which could lead to a challenge of disparate or discriminatory treatment. A significant area of litigation is the setting of impact fees and the approval for new development. If a developer challenges that fees that are proposed or the conditions imposed for the development, these items need to be set with objective standards which are independent of the public officials. Even though the public may have voice through public meetings in the approval process, the criteria set for the development cannot be made based upon criticism or clamor. An example would be if a business that provides counseling for disadvantaged youth was required to meet a more rigorous business license or permit process than other businesses in the area. Another area of caution is if public officials become involved in the operating details of the entity. The operating details are best handled by the professional managers that are hired to manage the day-to-day operations, who are intimately familiar with the policies and procedures of the organization. Exceeding Statutory Authority Public agencies are empowered to provide services within a territory, service area or boundary. They are also authorized to provide services according to their organizational charter and the budget that has been approved for those services. In the past, claims have arisen from agencies using those resources for an activity that is not in harmony with their statutory responsibilities. These types of claims may be avoided by crafting clearly defined agreements for newly developed services, interlocal cooperation or in providing services that are complimentary to other public agencies. Individual Official Committing the Entity to a Position Outside of the Normal Approval Process Public officials often form strong working relationships that are essential to completing the mission of their organization. Claims could arise if individual officials make statements to the public such as, “I think I can get the rest of the board to support this.” This can cause detrimental reliance due to one individual board members assurance and may not reflect a board’s ultimate decision. Even though elected officials can discuss the merits of a proposition, they should be careful not to promise or commit the entire board to an action. The best response is “thanks for your input, I’m sure the board will consider this in their regular board meeting.” Deciding Without a Fully Constituted BoardMost decisions are made in a full board meeting, after a thoughtful dialog and review process. At times, circumstances may lead to a meeting with an incomplete quorum. If an urgent decision must be made, it is essential to follow a process of scheduling and publicizing a new emergency meeting. Even if a decision made without a fully constituted board is later is ratified by a complete quorum, this decision may result in litigation. As these outcomes are often costly to remedy or defend, the best recourse is to schedule meetings with a full board, if possible. Meeting Ad-Hoc Outside of Board Meeting Board members may have social and business interaction outside of their official duties. If an emotionally charged or complex issue is pending for review, it may be easy to carry the item into open dialog outside of a board meeting, or in phone calls, emails, social media or other communication. The dialog and basis of official decisions must be part of the public record, for later review and discussion. If portions of the dialog are missing, it may be the basis for a potential error or omission claim. Violation of Open Meetings StatutesThe purpose of open meetings statutes is to provide greater transparency in the formulation of decisions made by elected or appointed officials. The statutes require notification, open access, and a record of the discussion of the meeting, which may be reviewed by the impacted parties of a decision. There are a few exceptions to the open meeting laws, with the most common being the discussion of sensitive personnel issues and litigation. An action taken by a governing body could be challenged if the open meetings process is not followed and recorded appropriately. Elected and appointed officials provide an invaluable service to their communities. Fortunately, challenges that result in public officials errors & omissions claims are rare as most follow the advice of legal counsel and avoid circumstances that could give rise to a claim. This allows public officials to perform their historic mission and provide significant service to their communities.
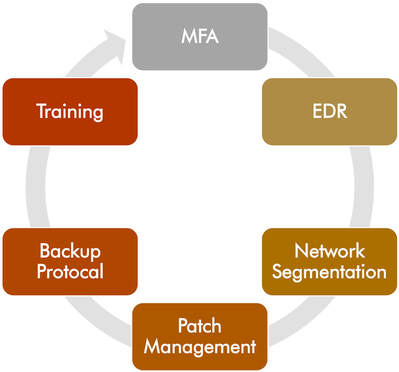
Over the last 24 months, the rate of ransomware attacks has skyrocketed in both frequency and severity, driving significant changes in the cyber insurance marketplace. In years past, the underwriting for cyber liability insurance was rather straightforward, and entailed just a few basic questions. Times have changed. These days, underwriters are requesting far more information related to ransomware prevention and IT risk management. In this article we’ll provide a deep dive into the current cyber security best practices required by underwriters. This will improve your cyber security posture and risk profile, and hopefully improve your ability to obtain comprehensive cyber liability insurance terms. It’s now common practice for underwriters to require that insureds have Multi-Factor Authentication (MFA) in place before providing terms. Without MFA, insureds are faced with significantly higher premiums and restrictions in coverage, including some insurance companies outright excluding coverage for ransomware events. What is Multi-Factor Authentication?Multi-Factor Authentication or MFA is a cybersecurity measure that requires users to confirm multiple factors verifying their identity prior to accessing a network or system. Generally, users must provide a password, verify access by inputting a code sent to another device, or confirm access with biometric data such as a fingerprint. Those hesitant to adopt MFA are often under the misconception that it requires the purchase of additional external hardware, software incompatibility or are concerned about potential user disruptions. While it’s true that MFA can require users to take an extra step or two at login, it’s not complicated and doesn’t always require buying new hardware or services. What should be protected with MFA? MFA should be used to protect remote network and email access as well as administrative access. This prevents system intruders from breaching networks to deploy ransomware, erase valuable data, or steal sensitive information for malicious purposes through a variety of commonly successful cyberattacks such as phishing or keylogging. MFA protects against:
How does MFA protect public agencies and utilities? Ransomware and social engineering occur daily. Such incidents can cost hundreds of thousands of dollars for even very small agencies, and require pricey forensic investigations that can take several weeks to complete. Such attacks often start with compromised login credentials. These credentials can be the weakest point of an organization’s digital footprint because employees often use the same password across multiple systems, create passwords that are too simple, share credentials with other employees, or inadvertently give information to cyber criminals. MFA protects businesses by adding a layer of security that can block 99.9% of attacks stemming from compromised accounts. For example, a phishing attack may obtain a user’s credentials, but be unable to provide the fingerprint or security question response required for authentication. MFA is already embedded in many products that many public agencies already use, including Office 365 and Google Workspace. For other systems a standalone MFA solution may be needed, common standalone MFA providers include:
Endpoint Detection and ResponseSince most attacks begin at an endpoint, companies should also be utilizing Endpoint Detection and Response (EDR), in collaboration with MFA, to maintain visibility into all endpoints. Employing MFA and EDR together will significantly minimize the threat of a breach, especially when combined with mature patching requirements, employee training, and increased awareness. Common EDR providers:
Network SegmentationNetwork segmentation is an effective way to protect IT systems from ransomware attacks. It refers to dividing a larger network into smaller sub-networks with limited inter-connectivity between them. By controlling traffic flows between various sub-networks and by restricting attacker lateral movement, network segmentation prevents unauthorized users from accessing the organization’s sensitive data and systems. Network segmentation is especially useful for organizations that need to comply with healthcare or financial data protection standards, e.g., HIPAA and PCI-DSS. Patch ManagementPatch management is a process that involves the acquisition, review, and deployment of patches on an organization’s systems. Simply put, patch management distributes and applies updates to your software whenever a vulnerability is detected. A patch is a piece of software code that improves an installed program – you can literally think about it as a “bandage” applied to software. Every time a security flaw is discovered or the program’s functionality needs to be enhanced, software developers create a patch to address these aspects. The need to completely redesign the program is therefore out of the question. Patches can be deployed to your entire infrastructure including software/operating systems, routers, IoT equipment, servers, PLC’s and more. System vulnerabilities have gained ground recently. Look at PrintNightmare that targeted Windows Spooler or the 16 years old vulnerability present in HP, Samsung, and Xerox print drivers. Or do you remember the notorious WannaCry ransomware attack? Well, it happened because of unpatched systems that ended up being exploited by malicious hackers. Even though Microsoft had released a security patch that addressed the vulnerability in Windows OS two months before the ransomware attack began, many individuals and organizations alike did not update their systems in time and thus remained exposed. Comprehensive Backup ProtocolIn order to ensure that your organization’s operations won’t be interrupted, that your data won’t be irretrievable, and you will not be held to paying an exorbitant ransom (which may, or more likely won’t, get your data back), it is critical that you have a comprehensive backup strategy that is tested frequently. Backup best practices include: Best Practice 1: Encryption Encryption is one of the most powerful ways to protect sensitive information. It works by converting the data into an indiscernible secret code. If an unauthorized party gets their hands on your data, they won’t be able to make heads or tails of it without your encryption key. For best results, your backup solution should protect your data both when it’s stored on a device or computer (“at rest”) and when it’s being sent and retrieved over networks (“in transit”) via encryption algorithms that meet industry standards – SSL/TLS in transit and AES-256 encryption at rest. This will prevent anyone other than authorized users from snooping, even a cloud provider hosting your data on their systems. Best Practice 2: Immutability Many of the major cloud providers now support object locking, also referred to as Write-Once-Read-Many (WORM) storage or immutable storage. Users can mark objects as locked for a designated period of time, preventing them from being deleted or altered by any user. Users should seek a backup solution that integrates seamlessly with this new object lock feature to create immutable backups. The backup solution should enable a retention period to be set for backups stored on supporting cloud platforms. Within this immutable retention period, backups can therefore not be deleted by anyone or anything, even if ransomware or a malicious actor acquires system credentials. Seek a backup solution that also provides powerful policy-based scheduling that predicts when backups will leave the retention policy and auto-protects any files that will no longer be retained, ensuring that you will always have point-in-time backups to restore within the immutable retention policy window. Best Practice 3: Air Gap Using an air-gapped backup solution is another important step toward optimal data security. Air gapping simply means storing the backup data in a different area that’s offline and physically separated from where it’s being generated. Since the data is stored in an air gap configuration, it is significantly more difficult for ransomware hackers or other illegitimate parties to intercept, gain access, and interfere with it. Historically, air gap storage was done with tapes, which required being physically stored offsite and secured. Another option today is a cloud-based destination that is not accessible with standard networking protocols, which ensures a separate backup that’s secure and inaccessible to hackers. Best Practice 4: Coverage Ensuring your backup solution covers your entire organization’s data infrastructure is paramount to recovering every piece of critical data after a ransomware attack. This coverage needs to include servers, endpoints, NAS shares, and cloud storage. Many agencies have certain older legacy systems that they rely on, so it’s essential to protect a wide range of operating systems, including older ones. If you need the data, you need a backup of it. No public agency or utility remains immune. The news continues to be littered with stories of organizations paying exorbitant ransoms, sometime into the millions of dollars in the hopes of getting their data back and their operations running again. And those are just the stories we hear about. There are countless others that never make headlines. The truth is, of course, the answer lies not in one silver bullet, but rather a layered defense designed to provide protection against ransomware, detection when there is infiltration, and in the event of a successful attack, robust backup process. Cyber Security Awareness TrainingEmpowering your employees to recognize common cyber threats is crucial to your organization’s computer security. Even with the best systems and procedures in place, employees are often the weakest link in our cyber security plan. Cyber security awareness training teaches employees to understand vulnerabilities and threats, and to protect themselves and the organization. Your employees need to be aware of their responsibilities and accountabilities when using a computer on your network. New hire training and regularly scheduled refresher training courses should be completed in order to instill the cyber security culture of your organization. At a minimum, cyber security awareness training should address:
In addition to the aforementioned cyber security best practices, there are additional steps which be taken to further improve the cyber security of your organization, some of these include:
Cyber Security Risk Management Resources
In March 2020, the Salt Lake valley experienced a 5.7 magnitude earthquake, centered west of Salt Lake City in Magna. While not a significantly large event, the earthquake resulted in over $100 million in damage to public infrastructure throughout the Wasatch front, including damage to schools, recreation centers, and water utility facilities, among others. It is anticipated that a large, 7.0 earthquake along the Wasatch fault would be 90 times more powerful than the earthquake experienced in March 2020. This would most likely result in far more extensive and widespread damage to public facilities and private property. Understanding how earthquake insurance responds and what is typically covered are crucial components to any public agency’s risk management and emergency response plans. Earthquake or Earth MovementWhile we use the term Earthquake often, the broader, more preferred coverage in this area is termed ‘Earth Movement,’ as it may also respond to claims arising from sinkholes, landslides, volcanic action and even manmade earth movement. For the sake of concision, we’ll use the term earthquake throughout this post. Scope of CoverageCoverage generally applies to those buildings and facilities that are scheduled on your insured statement of values, as well as up to 1,000 feet from these locations to cover incidental underground infrastructure and ancillary site improvements that may not be individually scheduled. The accuracy of your property schedule becomes even more crucial in the event of a large earthquake. If assets are undervalued or missing, you will most likely be unable to receive earthquake insurance benefits, even if you have sufficient earthquake limits available. Public agencies and utilities that take a more holistic view of earthquake risk planning often also include bridges, dams, large pipelines, diversion structures and other high value infrastructure. Most public agencies intentionally self-insure smaller, lower value utility transmission and distribution lines, due to the high cost of earthquake insurance, relative to the potential damage to these smaller assets. Insurance LimitsProperty insurance policies are typically written with a policy limit equal to the total insured or scheduled value, up to $500 million or $1 billion, for larger agencies. These limits apply to what is termed ‘All Other Perils’, meaning losses that are not otherwise excluded or sublimited. Most property insurance policies will sublimit earthquake coverage to a limit less than the policy limit. Due to the significant increased risk that a large earthquake would pose, insurance companies must limit their exposure to any single loss in order to maintain financial solvency, and ensure their ability to satisfy the claims of other policyholders. Probable Maximum Loss (PML) While the largest potential earthquake in our area would result in widespread damage, it would not damage all property beyond the point of repair. As seismic retrofit plans have been developed and completed in recent years, many facilities are far more resilient to earthquake damage. The Probable Maximum Loss or PML model is an incredibly valuable tool. A PML incorporates the most current geotechnical and seismic data, where your property is located, coupled with the construction details of your facility to determine the potential damage that could occur in the event of a large earthquake. Most PML reports use a return period of 475-500 years, meaning that within this timeframe, they express the anticipated maximum damage as a percentage of a buildings’ replacement value. After the March 2020 earthquake, seismologists determined that the Wasatch Fault is shallower than previously thought, meaning that shaking at the surface would be more intense (and damaging) than previously anticipated. This data is now being incorporated into PML reports, often increasing the anticipated maximum damage percentage. DeductiblesEarthquake deductibles generally apply on a per occurrence, per location or per building basis. In rare occasions, separate deductibles also apply to a building’s contents that are damaged as a result of an earthquake. Earthquake deductibles are generally large, to prevent small earthquake claims from eroding an insurance company’s capital base. Financial SecurityThe financial security of an insurance company could fill a separate post. However, for the purposes of this post, natural catastrophes – especially earthquakes, floods, hurricanes and wildfires can erode the capital base of marginal insurance companies very quickly when large, regional natural catastrophes occur. Insurance companies that have the highest ratings and financial size category with AM Best provide a greater level of security. While not all insurance companies are admitted in the State of Utah, those that are admitted provide an additional layer of security, as these insurance companies must satisfy regulators regarding the structure and adequacy of reinsurance, and underwriting methodology. Regulators also require insurance companies to have comprehensive PML modeling completed across their entire portfolios, to ensure that they will remain solvent and able to pay claims even after a large, regional earthquake. Case StudyMany public agencies had facilities damaged during the March 2020 earthquake. One stands out, and may prove to be a useful case study for other public agencies as they prepare and update their earthquake risk plans. In the summer of 2020, a city in the Salt Lake valley realized that one of their water storage tanks was being drawn down far faster than was typical in prior years, even on the hottest summer days. After thoroughly inspecting the tank, they determined that the outlet pipe from the tank to the water distribution system had been cracked, resulting in a significant leak. While a crack to the plumbing leaving the tank may sound like a minor issue, the repair entailed draining the tank, excavating the area around the tank, and replacing the piping and connections to the water tank, with the total cost to repair the tank exceeding $500,000. Fortunately, the city was well positioned with their earthquake insurance program, with the costs associated from the damage being covered. This situation could have been far different, if the city had not had coverage in a few key areas.
ConclusionWe hope this post provides a useful guide to better evaluate your own situation regarding earthquake insurance planning. We would welcome the opportunity to review any of these issues with you in greater detail.
Every year OSHA compiles a list of the ten most-cited standard violations from the previous year. OSHA publishes this list to alert employers about these commonly cited standards so they can take necessary steps to find and correct recognized hazards before an incident occurs. The 2020 fiscal year statistics, which ended Sept. 30th, have just been released and not surprisingly, the list’s actual violations stayed the same as the previous year, though some standards changed places on the list. Fall Protection remained in the number one spot while ladders rose one spot to number five. Respiratory Protection also moved up two places to number three on the list, while Lockout/Tagout dropped two places, from fourth to sixth. Let’s Take a Look at the Top three in more detail:
How to Avoid the Top Ten and Other OSHA CitationsDo any of the regulations on the list apply to your organization? If so, you should thoroughly review the standards and ensure you are complying with all employer requirements. There are several steps that an agency can take to both avoid worker injuries, illnesses and deaths. Developing and enforcing a comprehensive safety program is your key to success.
Your safety program should include:
|
Categories
All
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Contact220 Morris Avenue, Suite 340
PO Box 65608 Salt Lake City, UT 84165 (801) 486.1373 (877) 759.9935 |
Support |
© COPYRIGHT 2024. ALL RIGHTS RESERVED.
|